Authentication & Login
Secure access with multi-factor authentication. The console requires email, password, and a TOTP token to verify analyst identity before granting access.
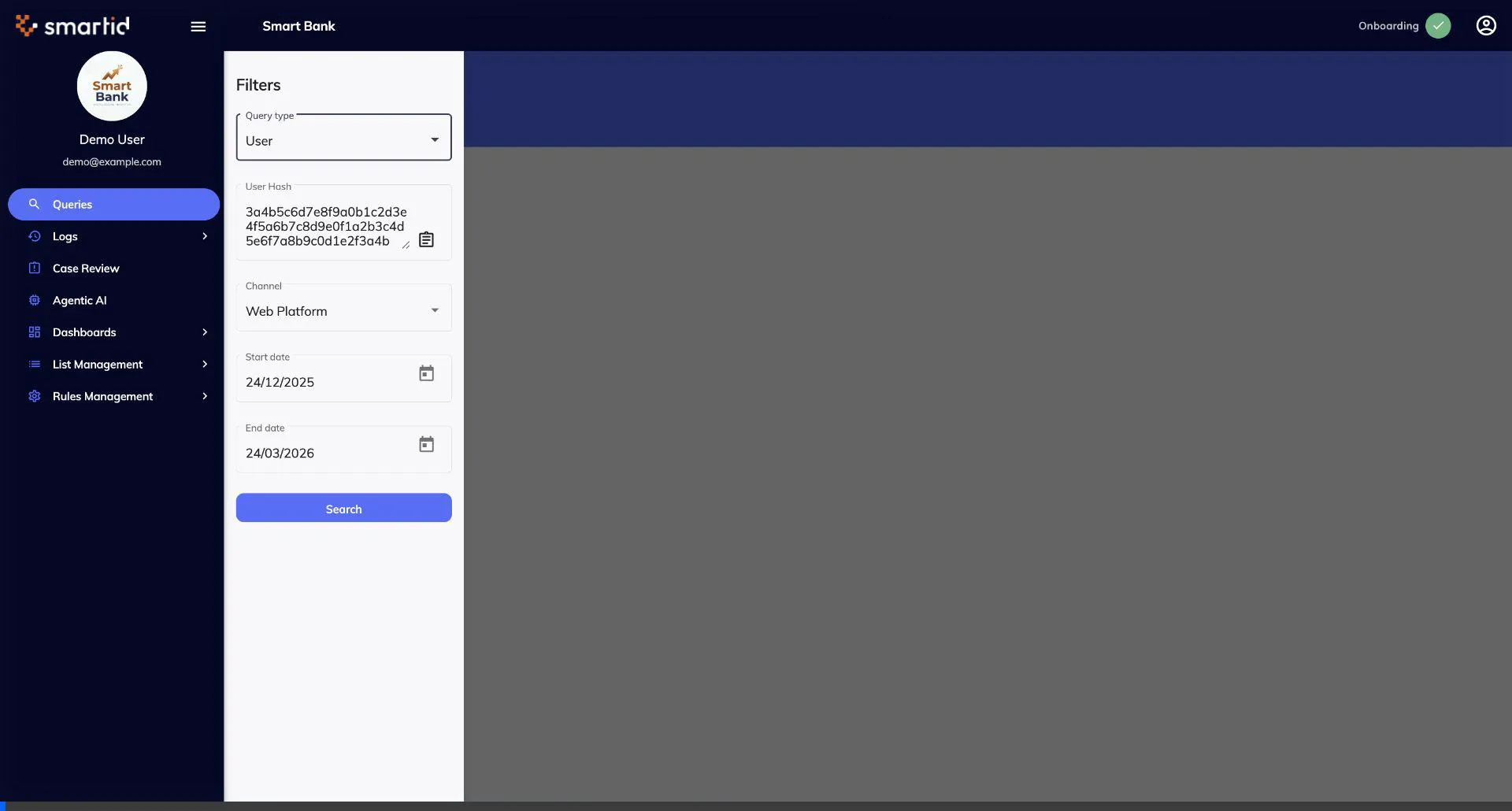
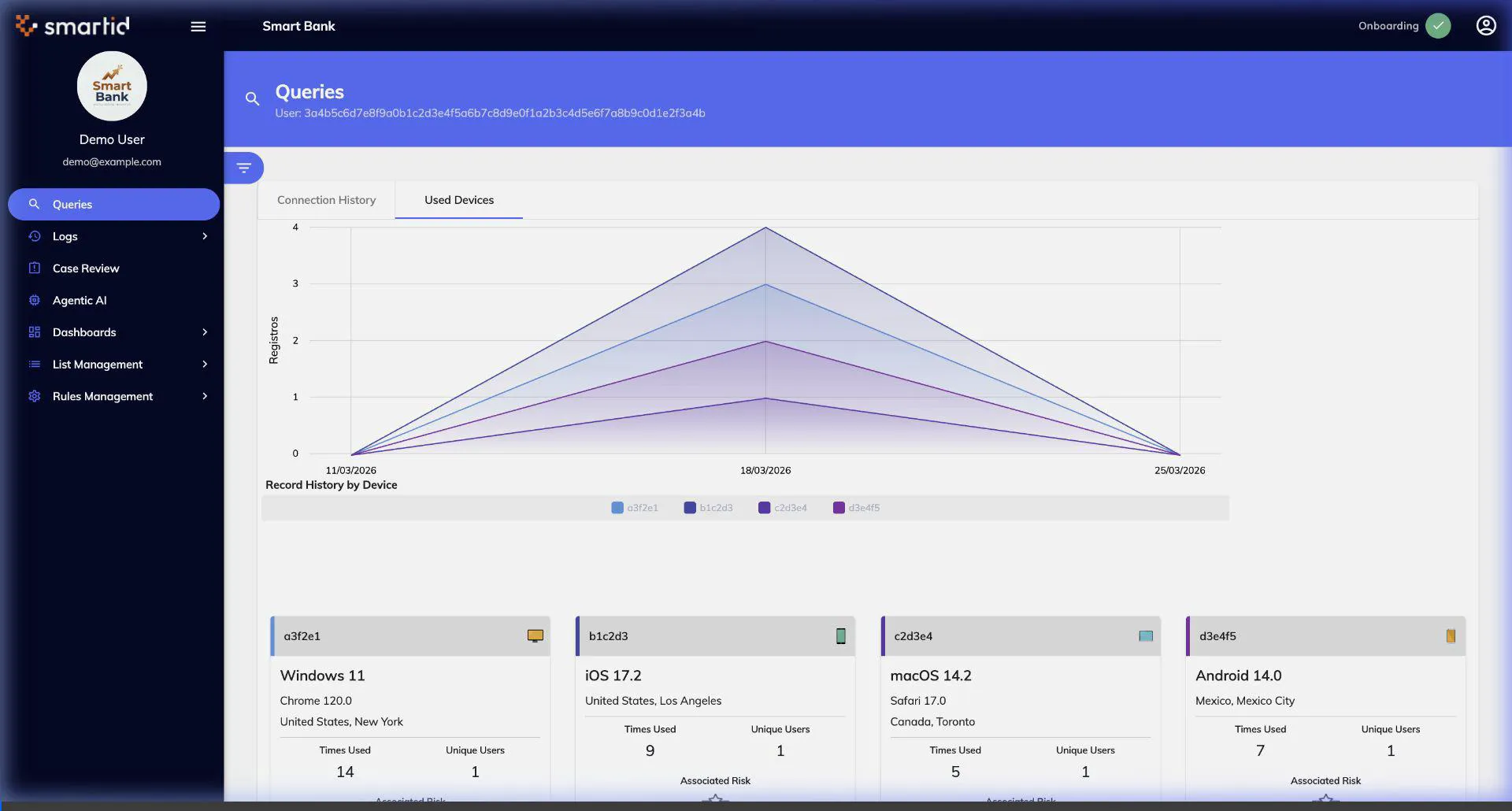
Queries — User & Device Analysis
Search and analyze user or device behavior. View connection history, detect device fingerprints, and identify cross-device patterns.
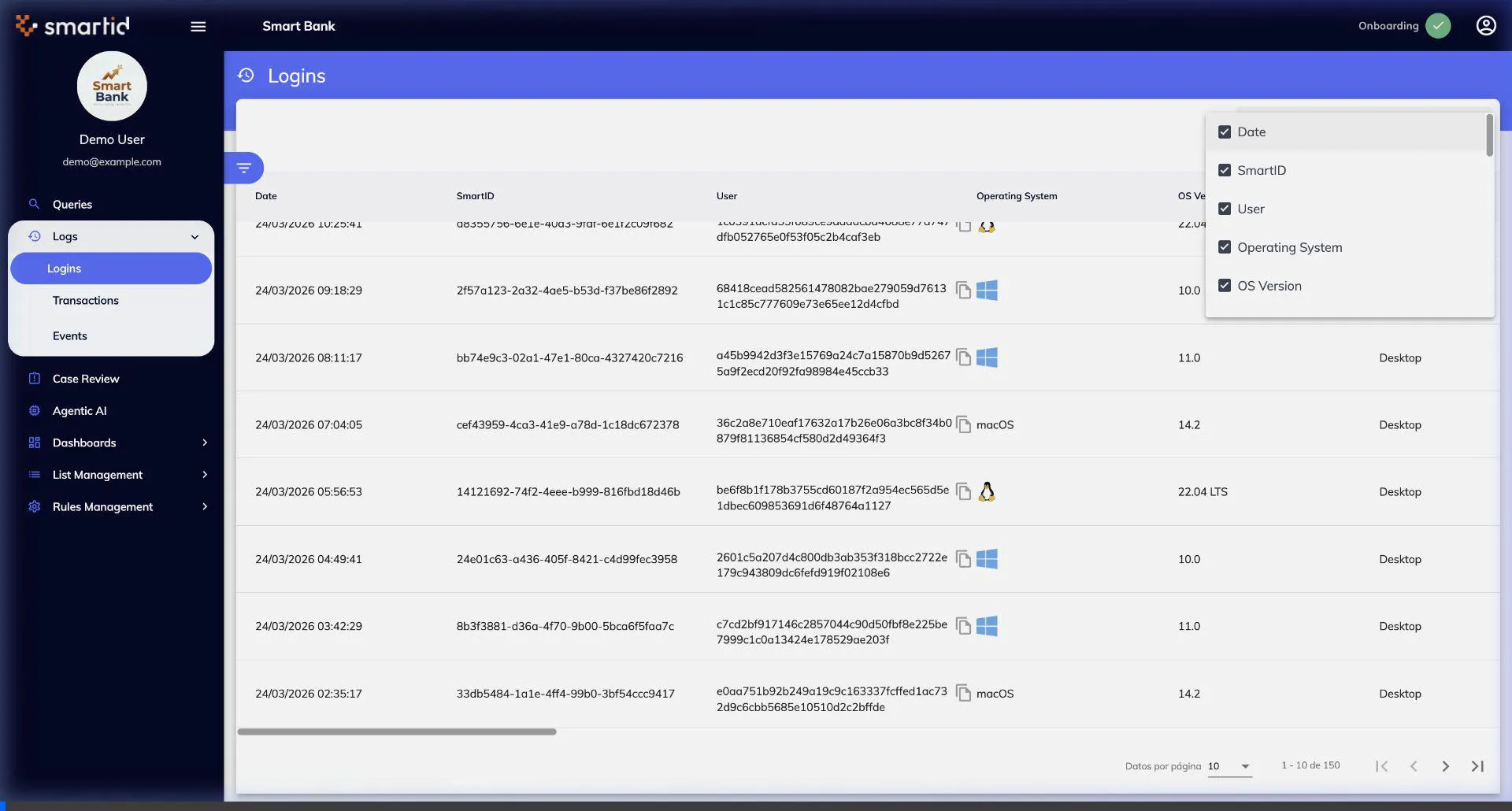
Logs — Logins
Review authentication activity with detailed login records. Apply date filters, search by user, and inspect columns including IP, country, and alert status.
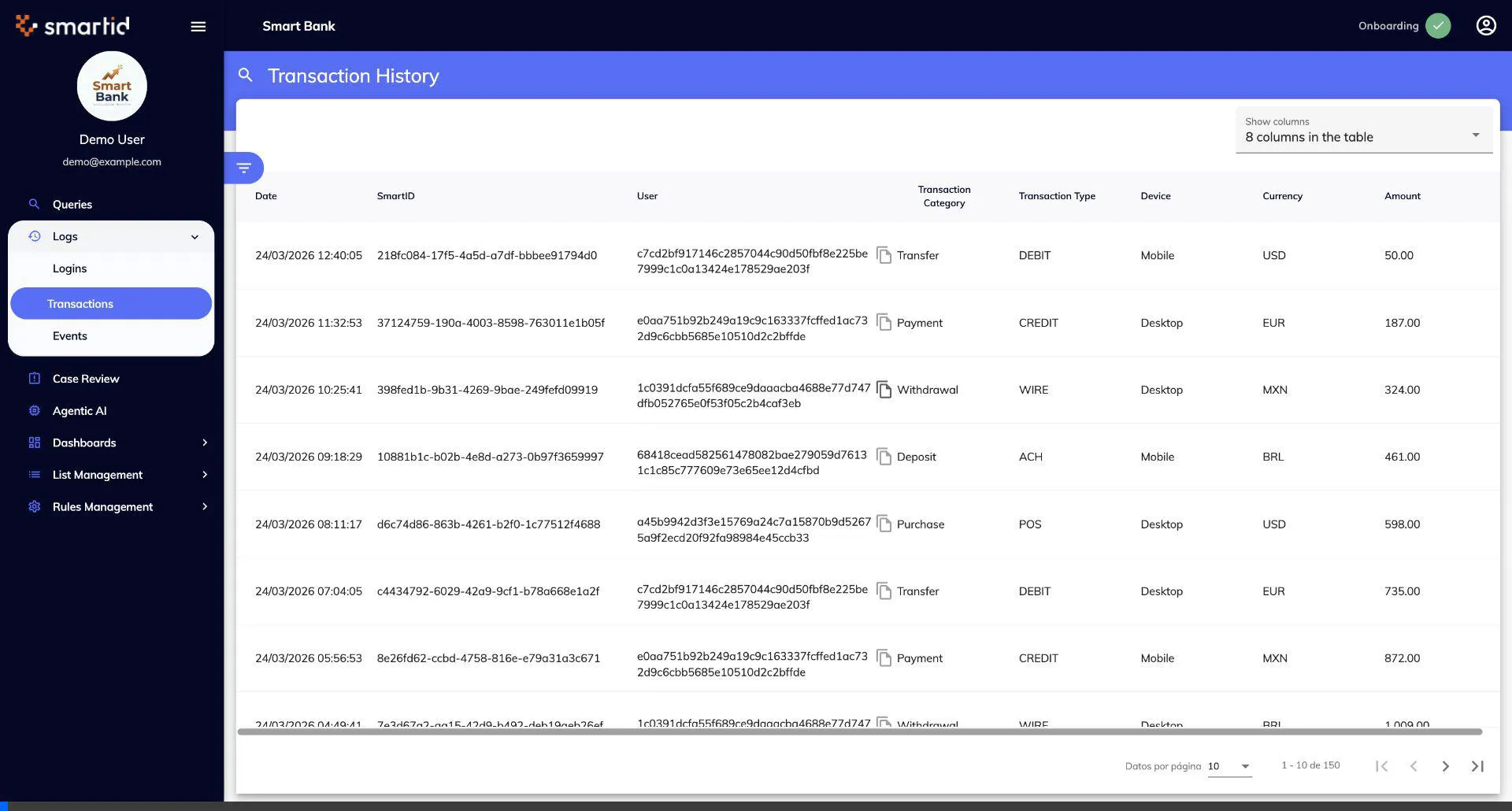
Logs — Transactions
Monitor financial operations in real time. Filter by date, amount, status, and risk score. Drill into individual transactions for full context.
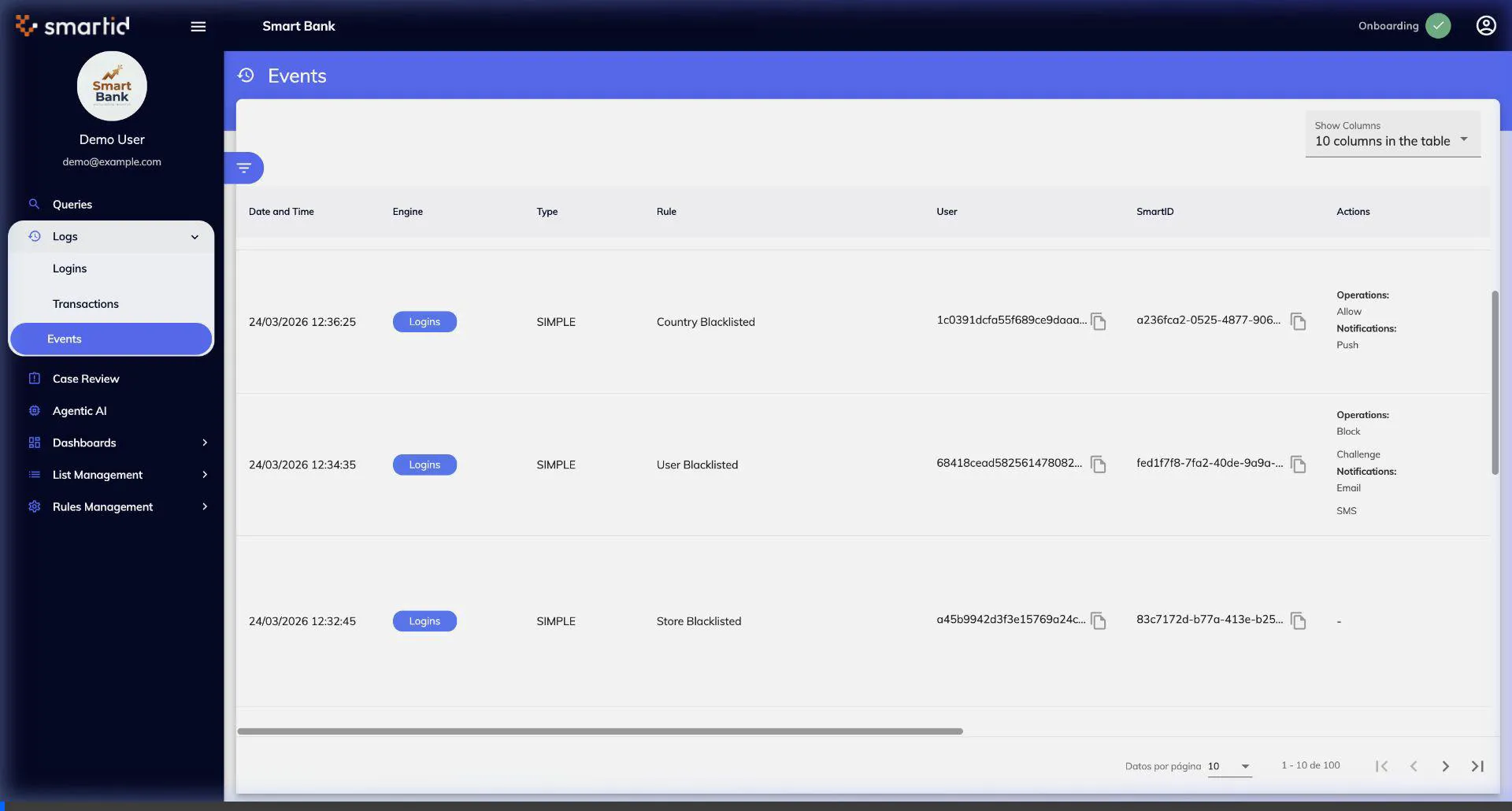
Logs — Events
Track system-wide events and behavioral signals. Events capture device changes, suspicious patterns, and automated rule triggers.
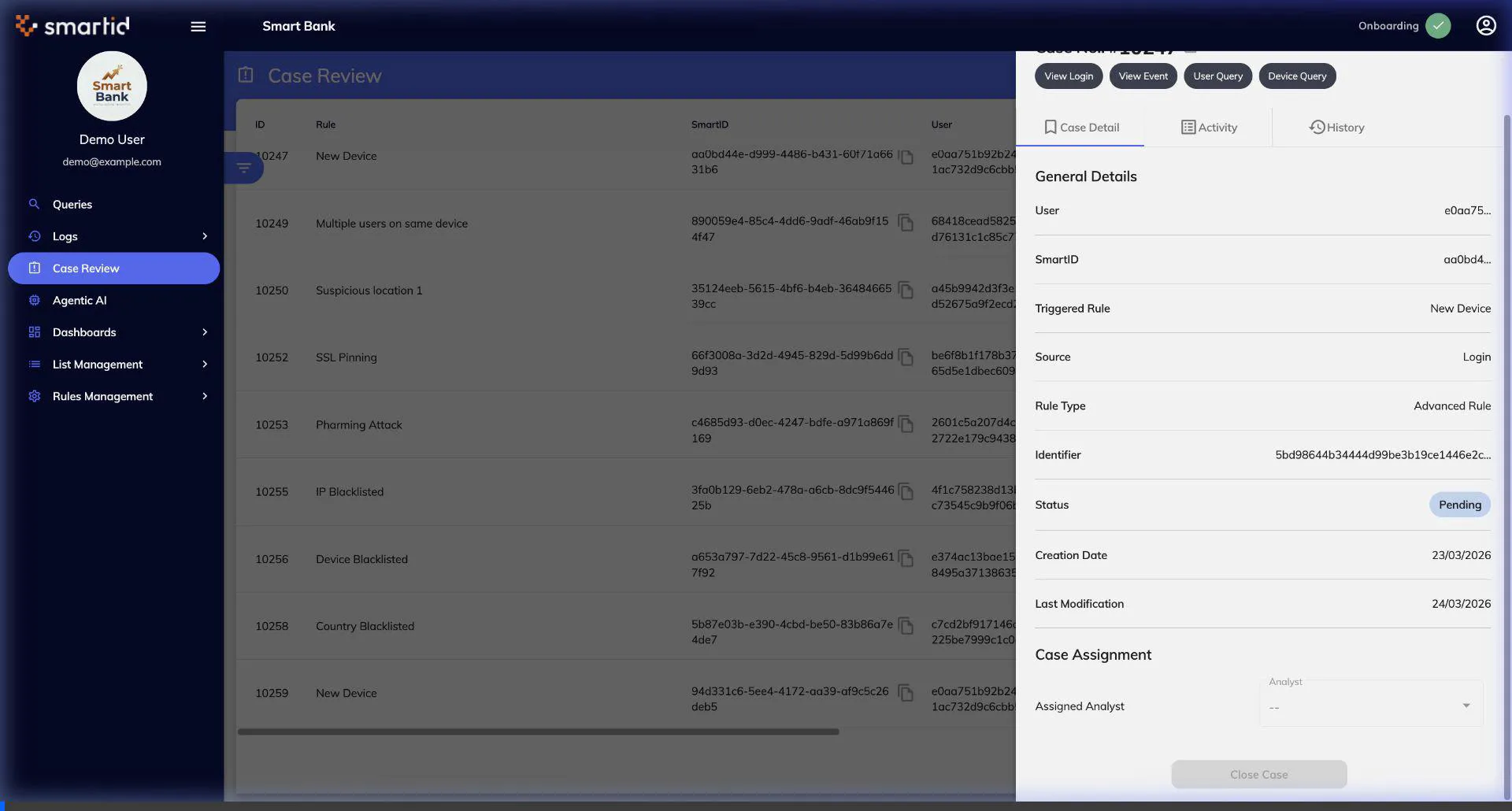
Case Review
Investigate flagged sessions with a comprehensive case management interface. Review risk scores, device data, and make disposition decisions.
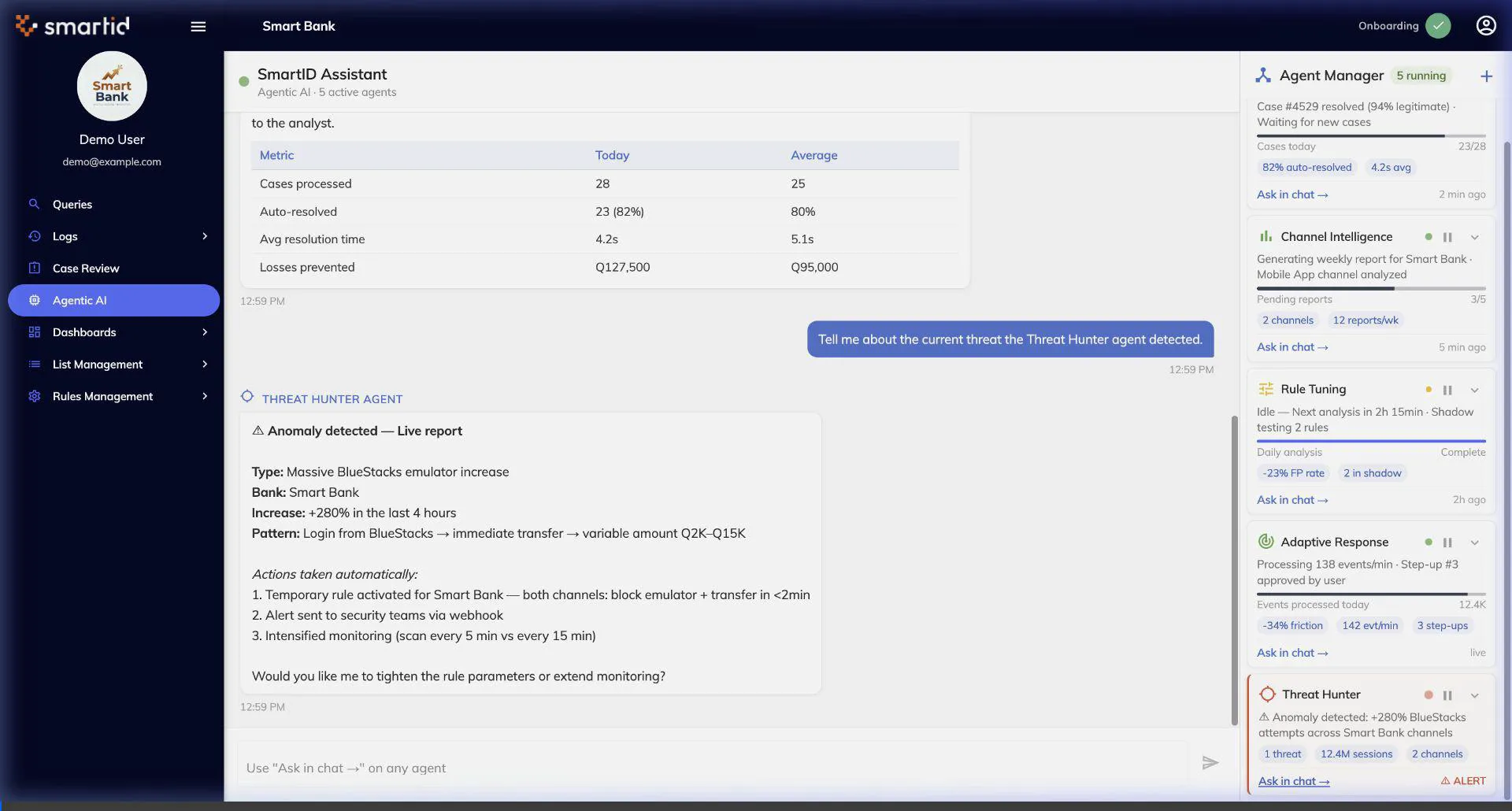
Agentic AI
Autonomous AI agents that monitor, analyze, and respond to threats in real time. Configure agent behavior and review autonomous decisions.
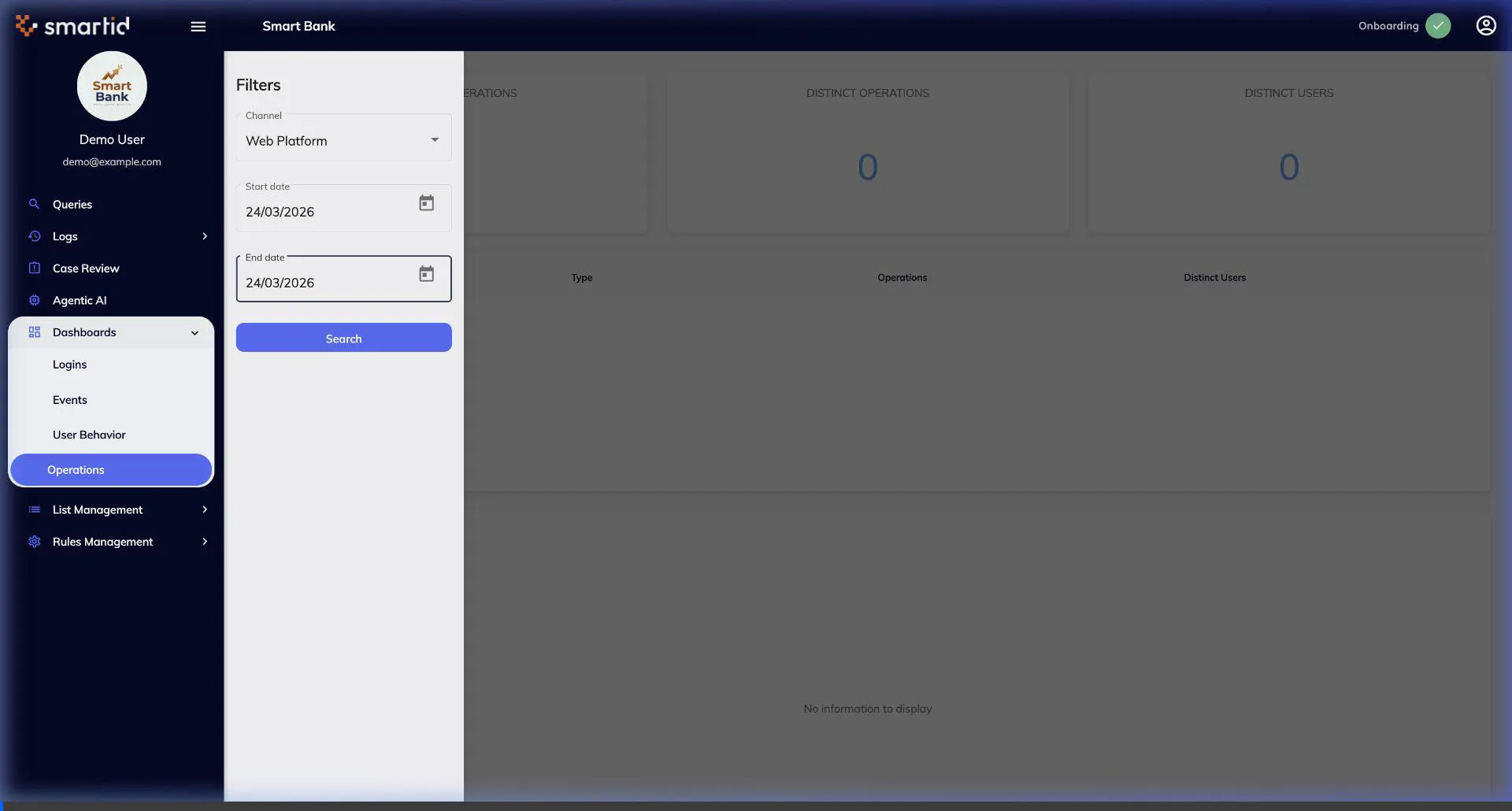
Dashboards
Visual analytics across all fraud detection dimensions. Real-time charts, geographic heat maps, and KPI summaries for executive reporting.
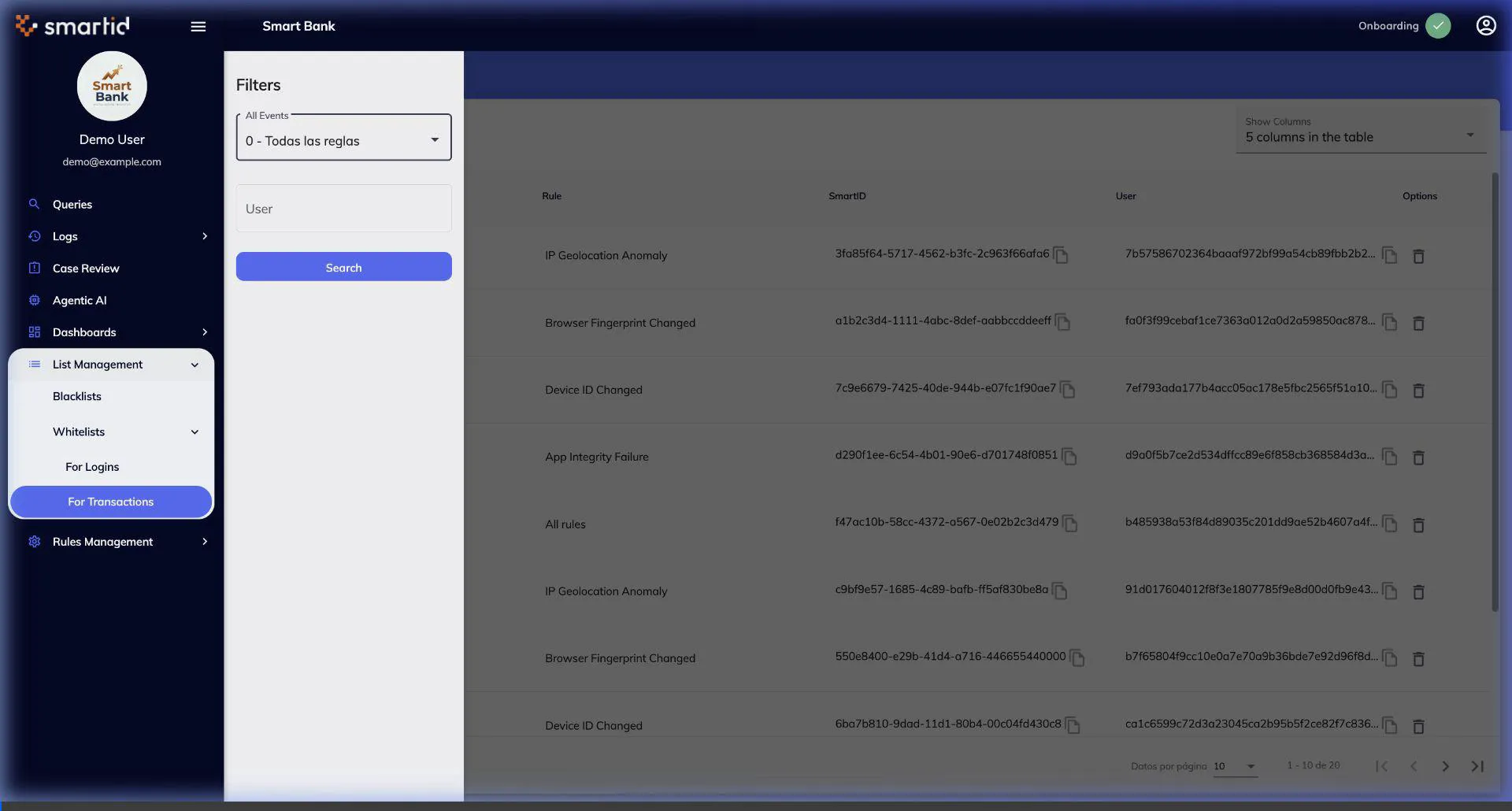
List Management
Manage whitelists, blacklists, and watchlists for users, devices, and IPs. Bulk import, search, and configure automatic list-based rule actions.
Rules Management
Configure detection rules with a visual rule builder. Create simple or compound rules, set thresholds, and define automated response actions.